CSPM + SSPM
Posture collection
Scan AWS, Azure, GCP, Microsoft 365, Google Workspace, GitHub, Okta, Auth0, Clerk and Azure DevOps from the same deployment.
Compliance On Demand brings Australian controls, cloud and SaaS posture, vendor intelligence, evidence automation and auditor review into a single-tenant deployment your team runs.
Assurance dossier
Control scope
In scopeE8, ISM, APRA, Privacy
Frameworks pinned, tailored and mapped to one control library.
Live sources
In scopeCISA, ACSC, SEC, Statuspage
Public vendor signals matched back to products and suppliers.
Evidence state
In scopeCollected, drifted, verified
Scheduled proof stays attached to controls and audit comments.
Vendor intel event
Live signalNew
18
Acknowledged
12
Verified
41
Platform map
The homepage now shows the product as an evidence system. Deeper pages carry the long-form search intent, while this view keeps the operating model clear.
CSPM + SSPM
Scan AWS, Azure, GCP, Microsoft 365, Google Workspace, GitHub, Okta, Auth0, Clerk and Azure DevOps from the same deployment.
GRC core
Track Essential Eight maturity, tailor ACSC ISM applicability and map evidence across APRA CPS 234, Privacy Act, ISO 27001, SOC 2 and NIST CSF.
Intel feed
Watch public sources for exploitable CVEs, Australian advisories, cyber disclosures and vendor outages that affect your supplier register.
Audit Hub
Invite external auditors into scoped engagements, answer control questions and export evidence bundles with verification status and comments.
External proof
Publish selected security material for customers, vendors and stakeholders without exposing the internal compliance workspace.
Inside the product
The central product object should feel like a real assurance workspace: scoped controls, current evidence, vendor events and auditor review status in one place.
Assurance workspace
Evidence collection
Today
73%
controls with current evidence
E8 patching
Evidence fresh
VerifiedACSC ISM 1501
Applicability due
ReviewAWS IAM root MFA
Scan passed
MappedVendor outage
New intel event
AcknowledgeProduct views
The site now uses captured product screens for the core workflows buyers ask to see: posture, Trust Portal publishing, audit review, vendor intelligence and document control.
Dashboard overview
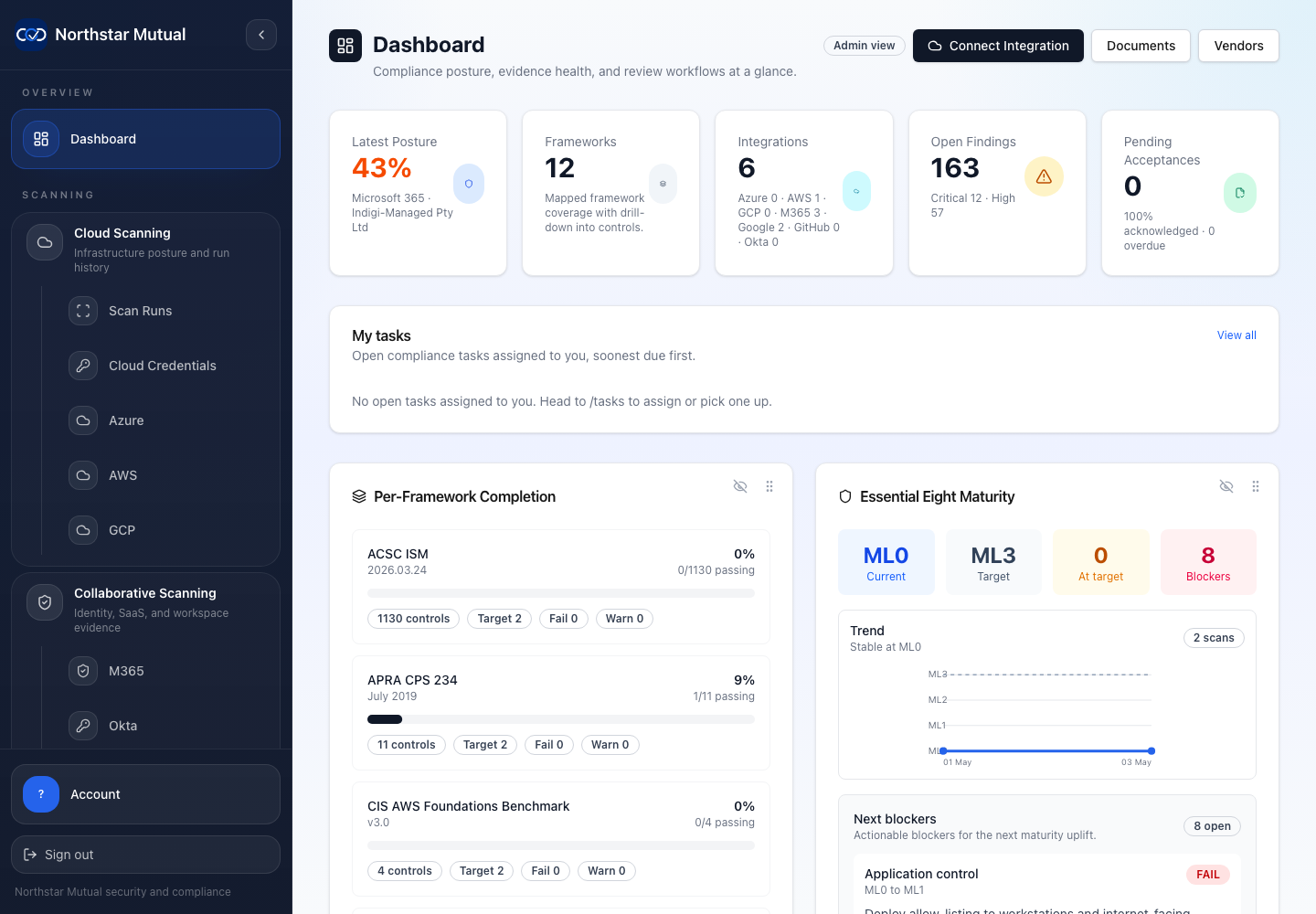
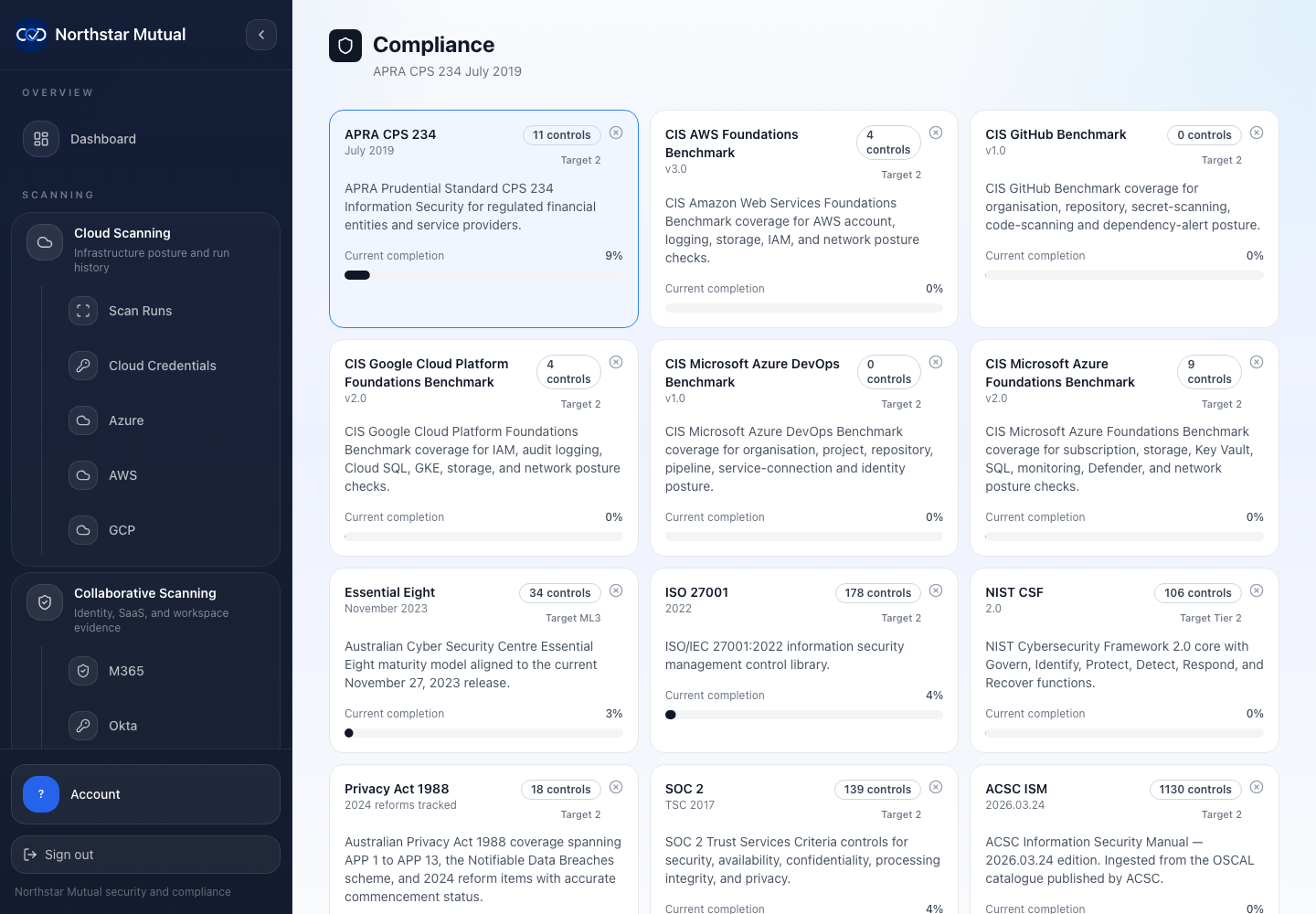
Compliance controls
Framework coverage, maturity targets, applicability and control-level evidence status.
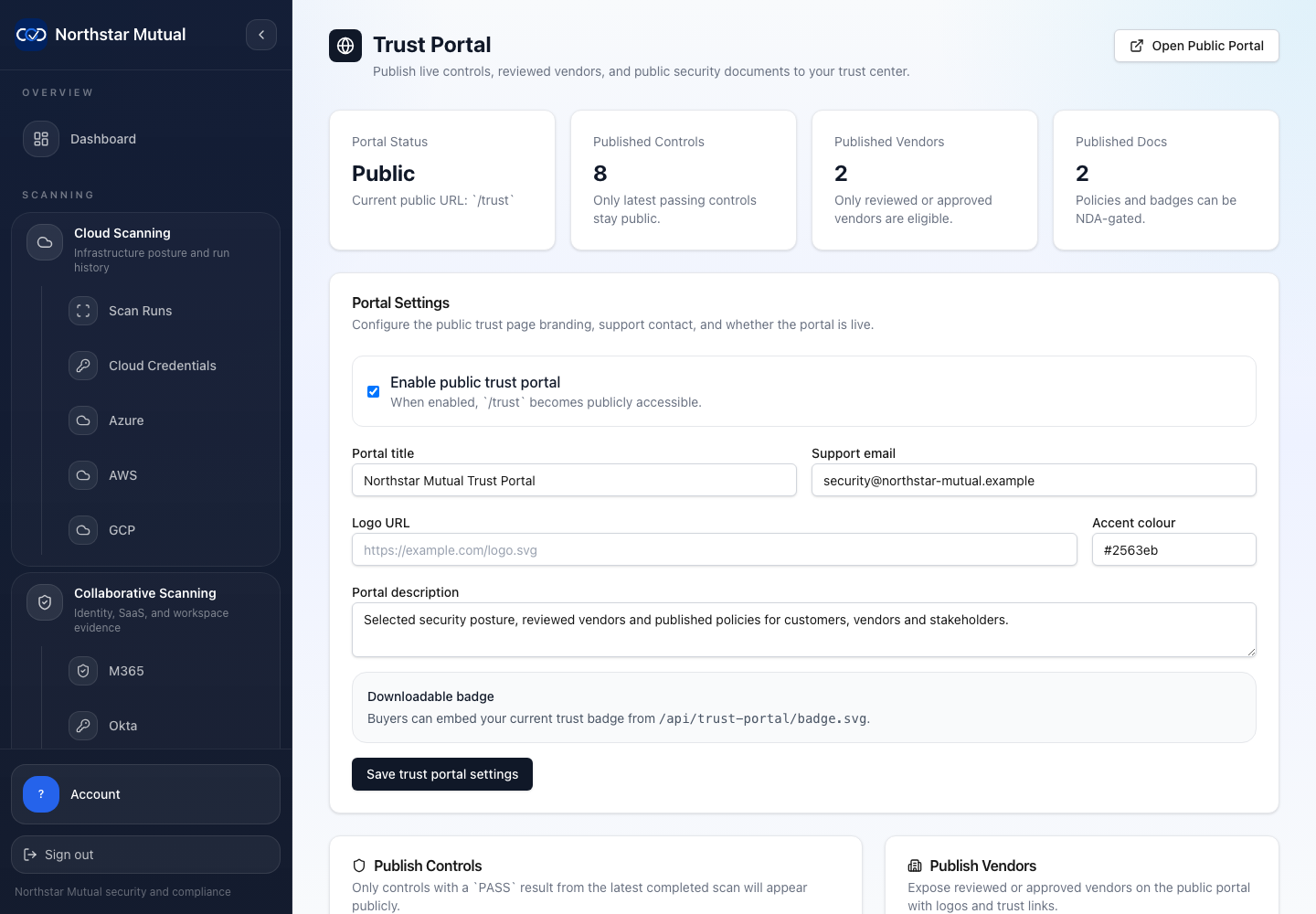
Trust Portal admin
Publishing controls, vendors and documents into a scoped external portal.
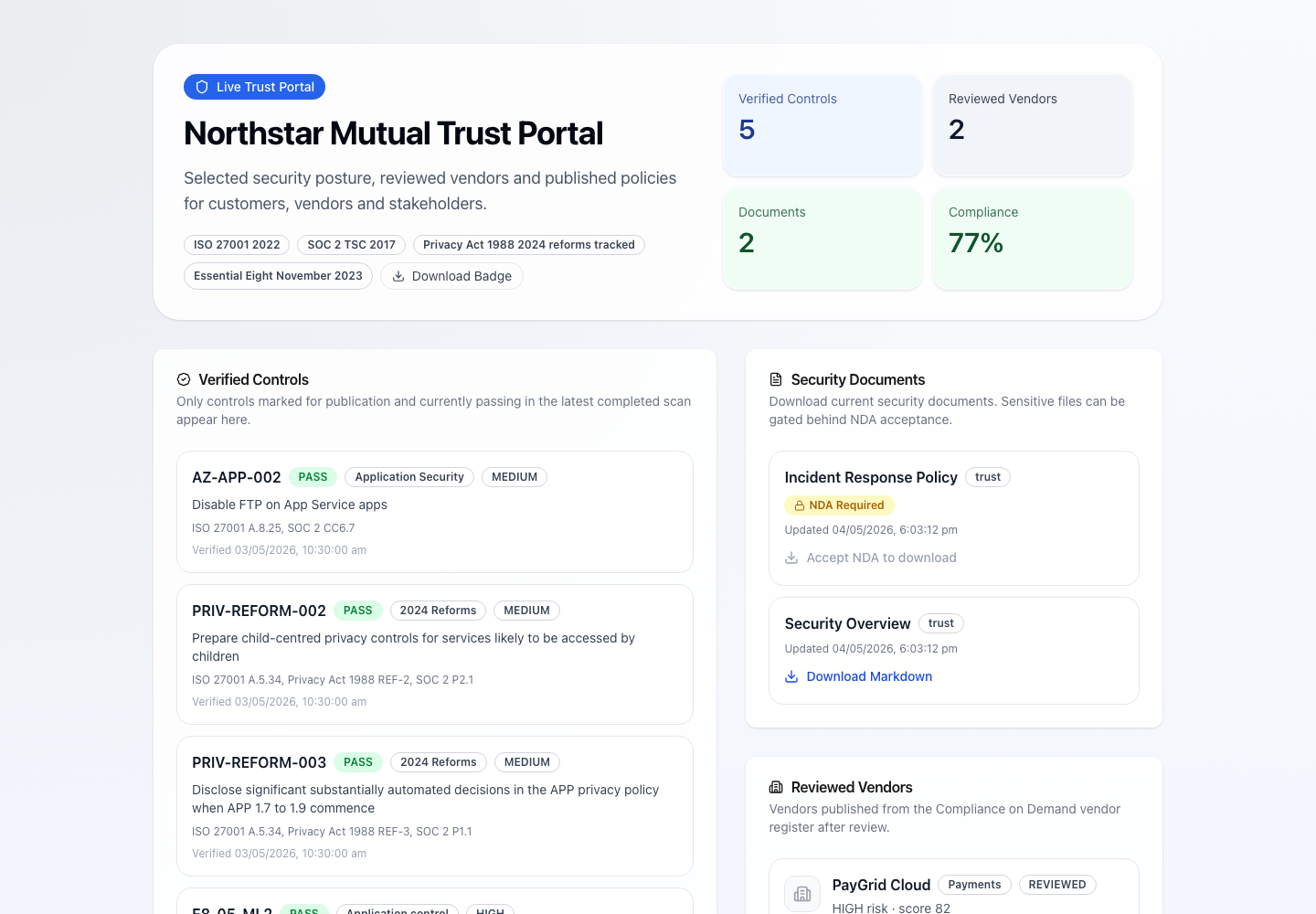
Public Trust Portal
Approved security material exposed without opening the internal evidence room.
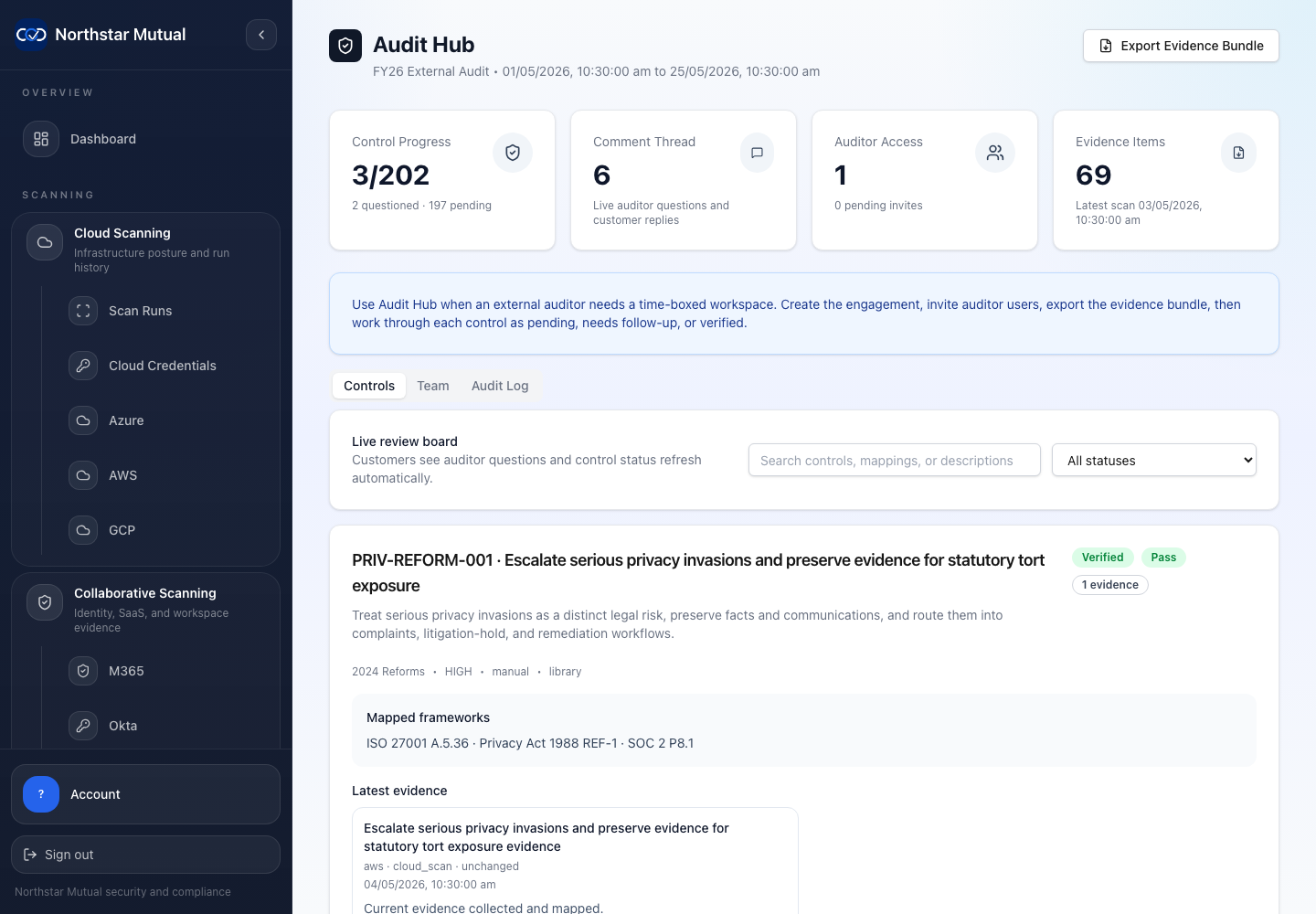
Audit Hub review
Auditor questions, control status and evidence review in one engagement surface.
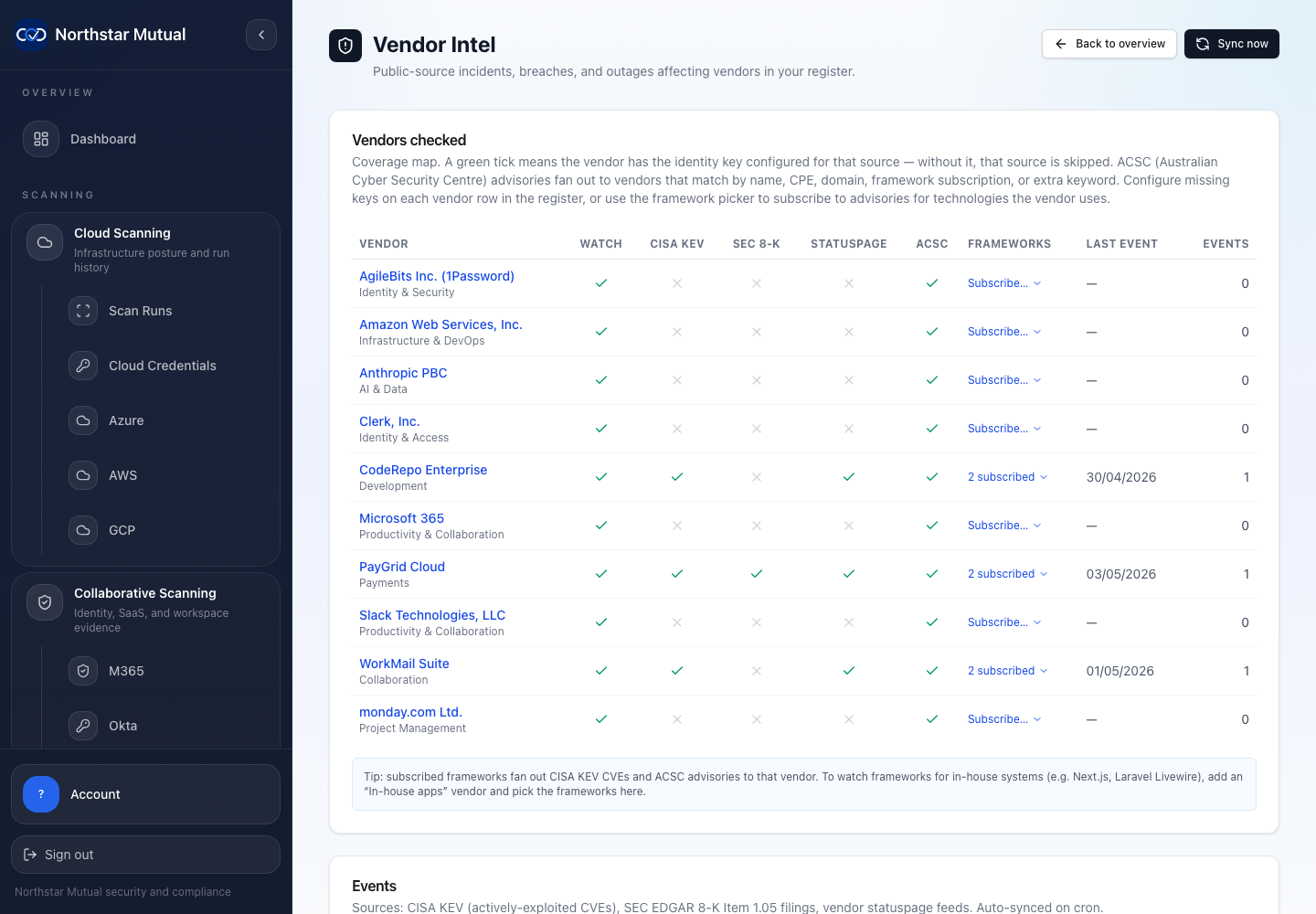
Vendor intel
Supplier risk context, public-source signals and review state attached to vendors.
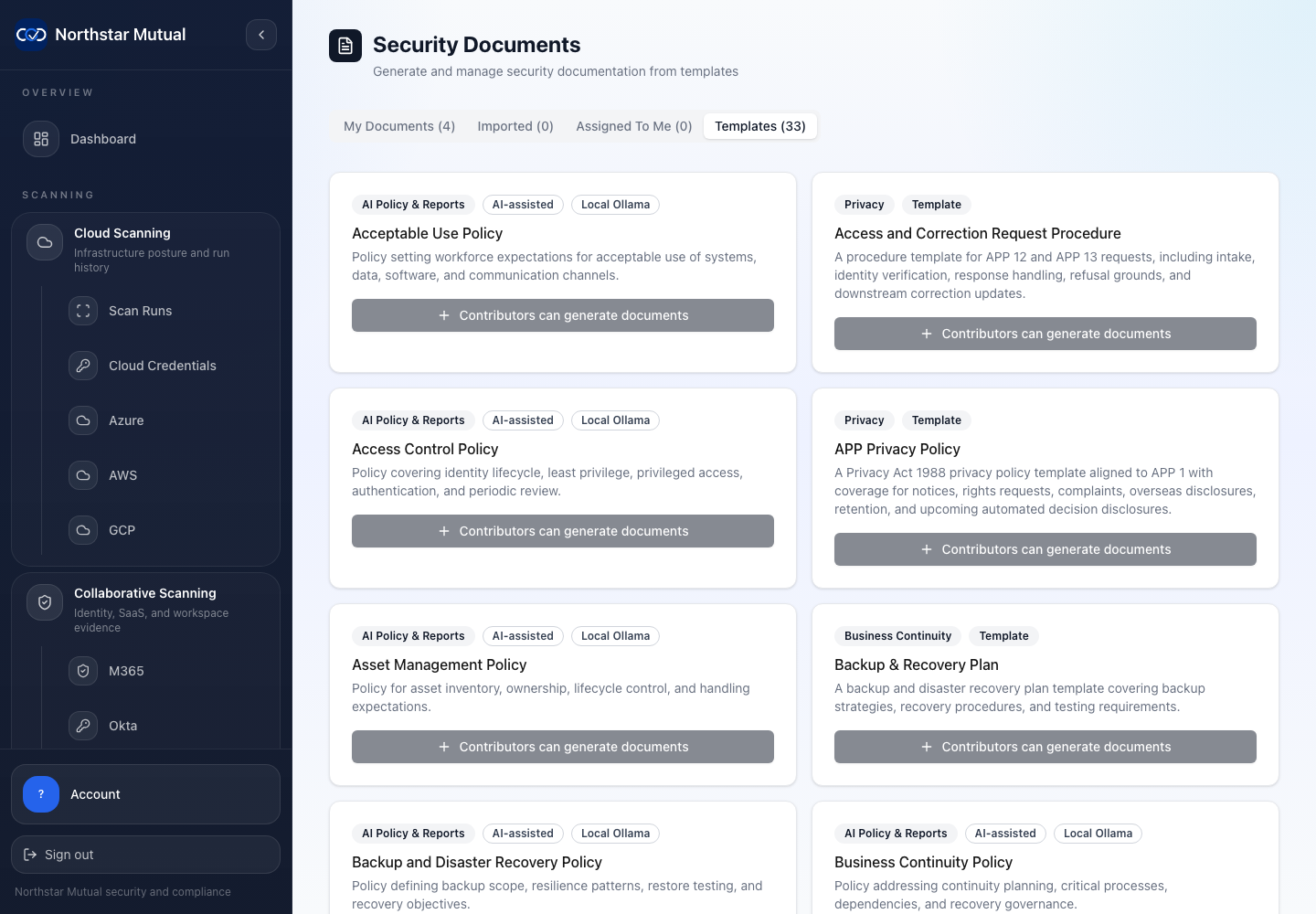
Documents
Published policies, generated material and controlled download paths.
Assurance workflow
Each stage keeps context attached: source systems, frameworks, evidence, vendor events, auditor comments and exportable records.
Choose frameworks, set maturity targets, decide applicability and define the systems in scope.
Add cloud accounts, SaaS tenants, identity providers, repositories, endpoint agents and supplier records.
Scheduled scans and evidence jobs keep control status, drift and mapped proof current between reviews.
Vendor intel events from CISA, ACSC, SEC and status pages are matched to the register.
Scoped engagements keep questions, comments and verification status attached to each control.
Generate assessments, evidence bundles, policies and Trust Portal updates from reviewed records.
Australian procurement
Compliance On Demand is developed by Yuma IT, a Canberra-based Indigenous-led technology company. For Australian Government and enterprise buyers working under Indigenous procurement targets, the platform combines sovereign assurance software with a verified Indigenous supplier pathway.
View Yuma IT on Supply Nation
Opens the public supplier profile used by procurement teams to verify certification.
Open supplier profileTrust Portal
Trust Portal publishing gives external viewers a controlled surface for approved security and assurance material, while internal records stay inside the self-hosted workspace.
Public view
A selected external view for customers, vendors and stakeholders who need security material without internal workspace access.
Internal boundary
The portal should expose only approved material. The evidence room, credentials, comments and raw collection detail remain inside the single-tenant deployment.
Sovereign by design
The self-hosted model is not a footnote. It shapes credentials, evidence custody, AI defaults, release hygiene and offline operation.
Docker Compose deployment with no managed SaaS control plane
Cloud credentials, evidence and generated documents remain on customer infrastructure
Bundled Ollama and Gemma option for local policy and report drafting
Air-gapped mode, offline release bundles and offline licence attestations
Cosign-signed GHCR images, pinned releases and SPDX SBOMs
Trust artifacts
Until there are public customer stories to cite, the strongest trust signals are operational: release hygiene, public sources, local AI options and evaluator-friendly resources.
Cosign-signed GHCR images, pinned versions and SPDX SBOMs support supply-chain review before deployment.
Selected security material can be published for external review without opening the internal compliance workspace.
Vendor events come from sources buyers can inspect: CISA KEV, ACSC, SEC cyber filings and vendor status feeds.
Policy and report drafting can use bundled Ollama and Gemma rather than defaulting to a third-party LLM.
Buyer routes
The homepage now behaves more like a mature product site: a concise front door that moves each buyer to the page that matches their question.
I need the product map
How CSPM, SSPM, control work, vendor intelligence and audit review fit together in one self-hosted product.
I need Australian controls
How Compliance On Demand handles Australian control work, maturity, applicability and regulator obligations.
I need vendor risk signals
How public CVE, advisory, disclosure and status feeds become acknowledgeable vendor risk events.
I need controlled deployment
Why credentials, evidence, generated documents and local AI stay inside the customer's boundary.
I need audit evidence
How scheduled evidence collection, drift detection and scoped auditor review reduce assessment scramble.
I need system coverage
Cloud, SaaS, identity, ticketing and collaboration integrations currently represented in the product positioning.
I need commercial fit
Commercial scoping for core deployments, MSP packaging and controlled-boundary enterprise requirements.
Buyer questions
Short answers stay on the homepage. Deeper explanations now live on focused pages that can rank for specific Australian compliance and self-hosted GRC searches.
Compliance On Demand is self-hosted Australian compliance and security posture software. It combines CSPM, SSPM, control mapping, vendor intelligence, evidence automation and auditor collaboration in a single-tenant deployment.
No. Customers run their own instance, so credentials, evidence, documents and audit records stay inside their infrastructure boundary.
The platform supports Essential Eight maturity, ACSC ISM tailoring, APRA CPS 234, Privacy Act incident workflows and cross-mapping to ISO 27001, SOC 2 and NIST CSF.
The product watches public sources including CISA KEV, ACSC advisories, SEC 8-K cyber incident filings and vendor status pages, then matches relevant events to the vendor register.
Yes. Trust Portal publishing is positioned for selected security material that customers, vendors and stakeholders can review without access to the internal compliance workspace.
Product briefing
Talk through deployment boundaries, frameworks in scope, vendor intelligence needs and auditor access requirements.